Unmasking the XZ Utils Vulnerability : CVE-2024-3094
Unmasking the XZ Utils Vulnerability :CVE-2024-3094 Evolution of Supply Chain Attack In recent trends, exploiting the supply chain has developed tremendously, as […]
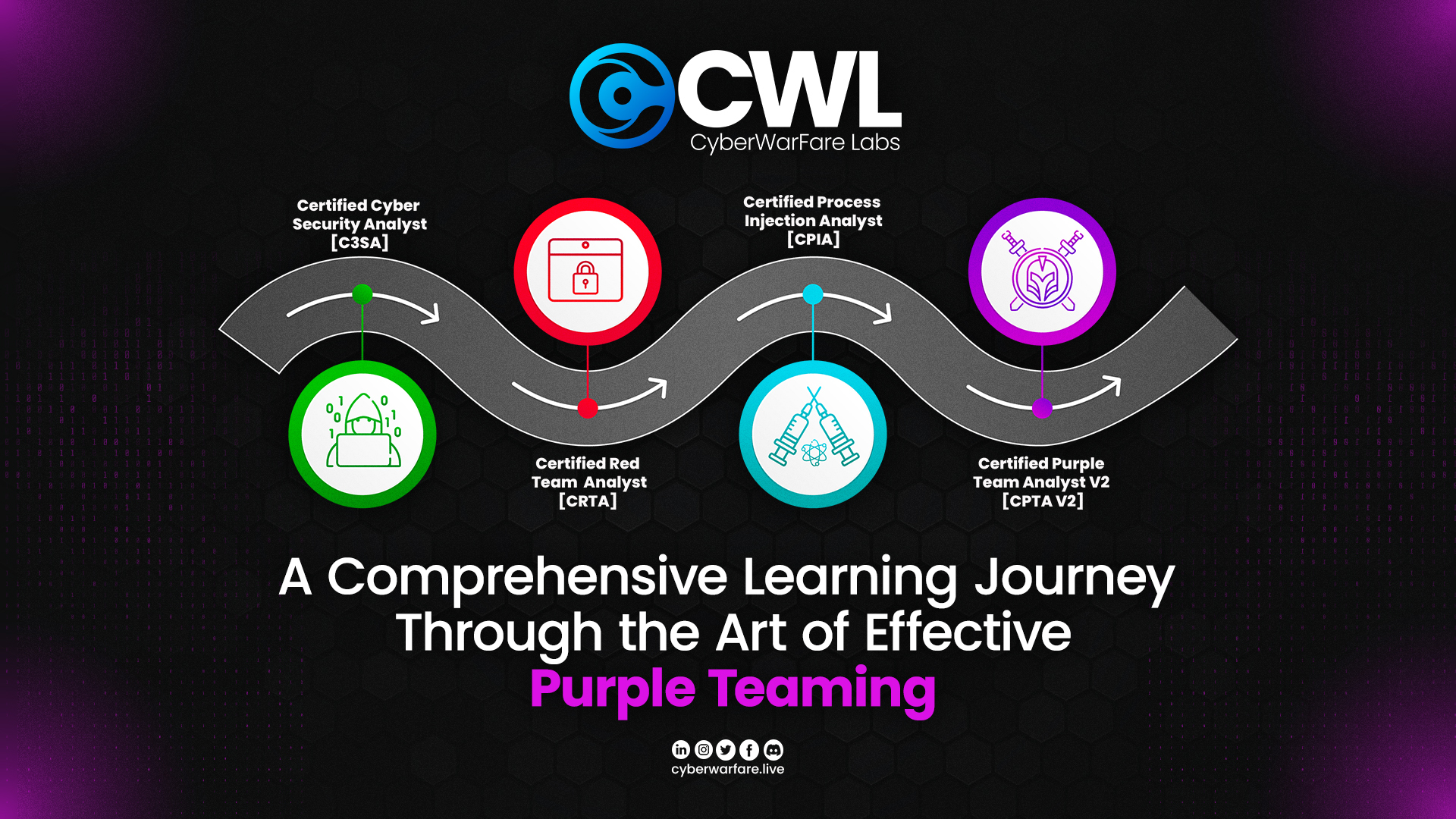
A Comprehensive Learning Journey Through the Art of Effective Purple Teaming
A Comprehensive Learning Journey Through the Art of Effective Purple Teaming Overview As we are aware that the Purple teaming is a […]
A Unified Purple Teaming Approach on WINRM investigation and detection
A Unified Purple Teaming Approach on WINRM Investigation and Detection OVERVIEW In this blog we will be discussing the unified Purple Teaming […]